Featured Blog
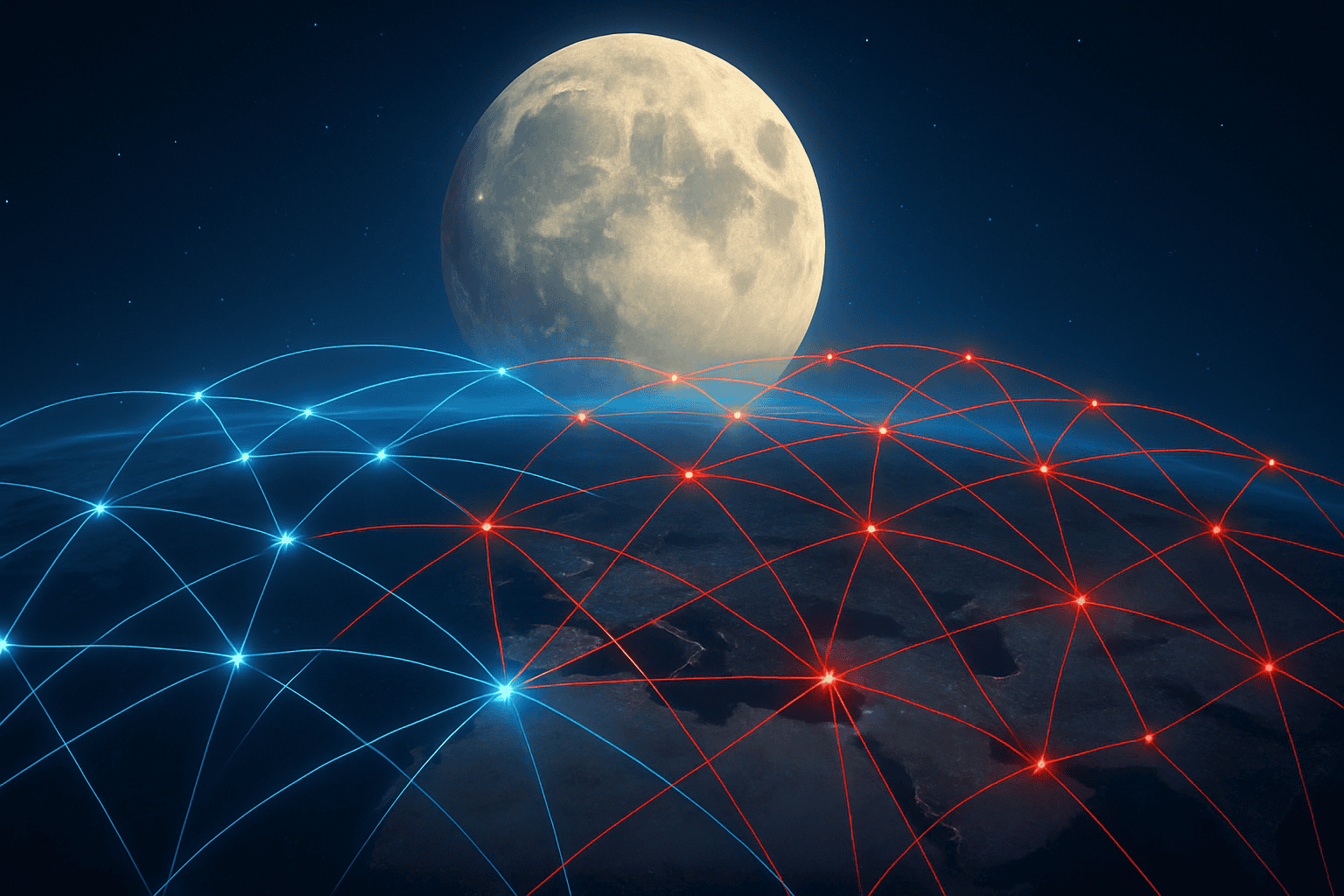
Network for Rent: How Outdated Router Security Fuels Cybercrime
Outdated routers are no longer just a nuisance. According to a recent FBI warning, they’ve become the launchpad for a global cybercrime infrastructure-for-hire. The culprit: TheMoon malware, which turns vulnerable routers into anonymous entry points for malicious activity. This issue highlights a critical area of cybersecurity that is too often overlooked: router security. This article […]
Cybersecurity Planning, Policy Development
4 Steps to Build Meaningful Visibility and Strengthen Your Cybersecurity Posture
Cybersecurity Planning, Policy Development
6 Steps For Building a Strong Security Culture in Your Organization
Cybersecurity, Policy Development
Solving 3 Common Security Gaps Through Better Cybersecurity Collaboration
Cryptocurrency, Cryptography, Data encryption
Cryptography 101: Demystifying Cryptography and Cryptocurrency & the Impacts on Cybersecurity
Cloud, Vulnerabilities
Protect Your Brand: 8 Social Media Security Awareness Tips to Combat Account Takeover Attacks
Attack Surface Monitoring
Why Continuous Attack Surface Monitoring Should Be A 2024 Cybersecurity Goal
Breaches, Cybersecurity Planning, Employee Cybersecurity Training, Incident Response, Tabletop Exercises
Our Top 3 Evergreen Incident Response Tabletop Exercise Scenarios & Why These Should Be Part of Your Cybersecurity Plan
Cyberattacks, Cybersecurity Planning, Incident Response, Incident Response Testing, Tabletop Exercises
Our Top 2 Cybersecurity Tabletop Exercise Examples for 2024
Employee Cybersecurity Training, Security Controls Reports