Top 10 Cybersecurity Program Design Activities & Tips to Improve Your Cyber Maturity

This blog is designed to help organizations in the early-to-mid range of the cybersecurity program design. This includes companies that are ready to structure existing controls into a comprehensive, enterprise-wide cybersecurity program, or those with a lot of good components in place already who want to improve their cyber maturity.
We’ll take a look at 10 key areas you should be thinking about, and then touch on how to approach maturing and formalizing your program to improve your overall cybersecurity posture.
Popular Cybersecurity Framework Foundations
Known cybersecurity controls frameworks are great resources for cybersecurity program development. The NIST Cybersecurity Framework, NIST SP 800-171, and ISO 27001 are all comprehensive options. However, these frameworks are long and detailed, with 100+ individual controls each, so they may be overwhelming at this stage in your journey and better leveraged as references for best practices in specific control areas.
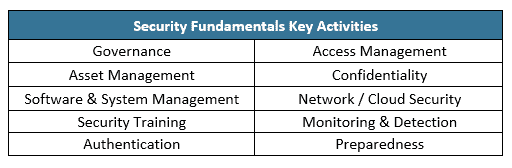
Top 10 Activities to Include in Your Cybersecurity Program Design
To provide a framework that may be more manageable for some organizations, our consultants used our knowledge of widely used frameworks, common threats, and best practices to identify 10 key activities we think are essential to include in an enterprise cybersecurity program.
- Governance: Who’s steering this ship? An effective cybersecurity program requires consistent and visible management support and engagement. Your program also needs clear roles and responsibilities for cybersecurity tasks and program development. Internal reporting on monitoring efforts ensures organizational awareness of current risks and provide transparency regarding remediation efforts and outcomes. External resources should be used to support program development and continuous improvement.
- Asset Management: Securing your organization’s assets starts with knowing what is on your network, both hardware and software. Processes need to be established to manage the introduction of new assets and software, harden all assets, and to ensure secure destruction when assets are no longer needed. Read more on this topic in 4 Key Steps to Creating an Effective Cybersecurity Plan.
- Software & System Management: Outdated and unpatched systems are easy targets for attackers. Establish regular processes for checking for and applying patches and have monitoring in place to ensure the processes are being followed as intended. Read our blog on software patch management to learn common mistakes and how to fix them.
- Security Training: People are essential for securing an organization’s assets and data. It is important to equip them with awareness of common threats and how their actions and decisions play an essential role in the organization’s security. Building a security aware culture needs to be an ongoing effort, not just initial awareness training at onboarding.
- Authentication: Effective technical access controls are essential for protecting the confidentiality, integrity, and availability of data. Technical controls include strong password policies, secure password storage, and consistent use of multifactor authentication.
- Access Management: Managing who has access to what data and systems should include processes such as access authorization, account review, and consistent steps for access termination. Organizations also need to implement role-based access and restrictions on administrator privileges.
- Confidentiality: First you need to identify what data is considered sensitive in your environment and where is it stored. Then you can establish guidelines for who can access the data and how the data is stored, transmitted, and destroyed.
- Network / Cloud Security: Secure network design, implementation, and management is essential to protect your systems, data, and organization. Network security considerations include architecture, boundary protections, change management, and the ongoing identification of vulnerabilities through regular scans or technical testing. Cloud environments need secure configuration, change management, and ongoing monitoring.
- Monitoring & Detection: If your environment is experiencing a security threat, how will you know? Timely detection of unusual activity requires knowing what normal looks like for your environment, which can be supported by tools and monitoring, either managed internally or outsourced. Watch this on-demand video on proactive monitoring and logging.
- Preparedness: Cybersecurity is often focused on preventing cybersecurity incidents and protecting sensitive information. However, it also needs to consider what systems, either on premises or in the cloud, are critical for business operations and how to ensure continued availability of those systems. While preventing a cybersecurity incident or outage is an essential goal, organizations also need to be prepared to deal with an undesired situation. Key areas for preparedness include incident response planning, availability / continuity planning, and cybersecurity insurance coverage.
Tips for Improving Your Cybersecurity Program
Now that you have a list of the key activities, here are tips from our advisory team on how to mature your cybersecurity program and improve your overall cybersecurity posture.
Here are a few tips:
- Consider addressing one topic at a time to keep the project manageable and ensure you can move each item forward at a good pace.
- Activity #1 Governance is the logical starting point for cybersecurity program design, as establishing management buy-in and support will form an essential foundation for your cybersecurity program design project.
- After that, pick the order that makes sense for your organization. Consider your mission, top cybersecurity concerns (i.e., sensitive data, system availability), and any history of incidents you want to prevent going forward, such as business email compromise or ransomware. Start with the topics that seem most impactful and relevant for your organization to be sure you gain high-value traction early in the project.
- Convene organizational stakeholders and those whose roles align with the activity to talk through existing controls and processes, as well as consider if they are meeting your organization’s cybersecurity needs. For example, #6 Access Management will need involvement from human resources, hiring managers, and the IT roles who grant access to systems and data.
- Consider if processes are followed consistently. We often encounter situations where processes are in place, but they are not always followed. Using #6 Access Management as an example, we may see delayed personnel separation notifications from human resources to the IT department, resulting in delays in IT disabling access to email and cloud applications, creating a risk of unauthorized access.
- Identify ways your processes could be improved. The inconsistent access control example may need a documented, required process plus training and spot checks to improve consistency. Reference known frameworks, like the NIST Cybersecurity Framework, for guidance in specific areas.
- Document it. Developing a written security program can feel daunting. I like to advise clients to keep it simple at first. Policies and program documentation don’t need to be formal or fancy to provide value. Start with simple checklists, or informal bullet points describing process and roles and responsibilities. Simple, shared documentation on these topics can go a long way in establishing a shared understanding of cybersecurity requirements and providing a reference for agreed-upon processes and standards.
We hope that these tips help you with your cybersecurity program design or growth. If this still sounds like a lot to tackle, LMG Security’s experienced consultants can help. Our advisory engagements start by understanding your organization’s mission, priorities, data, and environment. We then talk through existing processes and cybersecurity controls to identify any gaps and make recommendations on your cybersecurity program design, as well as ways to reduce risk and improve your overall cybersecurity posture. Contact us if you would like help.

