Featured Blog
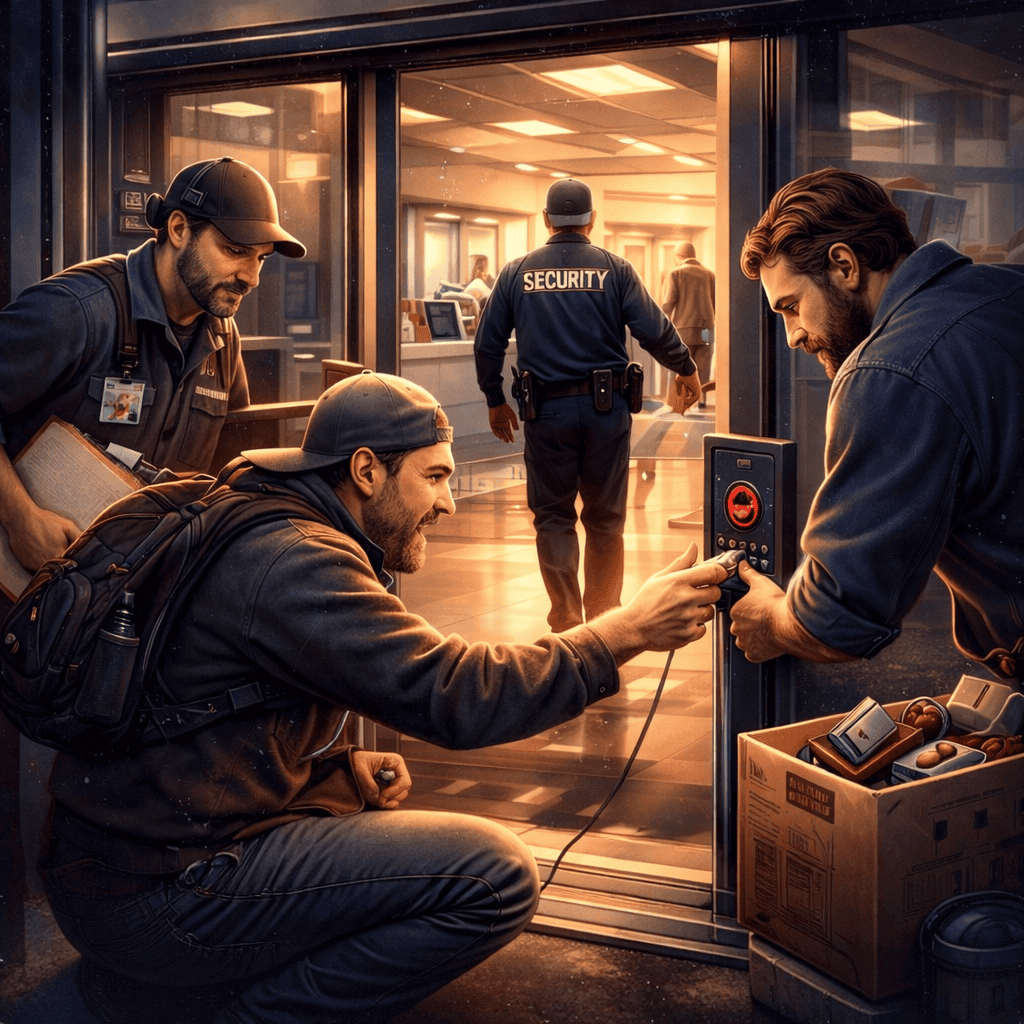
Access Granted: Why Your Strongest Controls Fail at the Front Door
In a recent Cyberside Chats discussion, LMG Security’s penetration testing team described how they routinely gain access to corporate environments not through exploits, but through people. One recent engagement illustrates the point clearly. As part of the test, the client hid a series of Easter eggs throughout their building. Not digital artifacts, physical objects placed […]
Black Hat, Cyberattacks, Cybersecurity, Malware, Network Forensics, Vulnerabilities
Antivirus Evasion
Breaches, Cyberattacks, Cybersecurity, IT, Malware, Network Forensics
LMG wants to help you Achieve NOTHING!
Cyberattacks, Cybersecurity, Malware, Uncategorized
Industroyer: The Resurgence of Industrial Controls Malware
Compliance, Cybersecurity, Partnerships