Black Hat - Network Forensics Highlights
 Ah, summer– when hackers migrate to Las Vegas to renew friendships, obtain bleeding-edge training, and release their latest exploits and security research. Every year, LMG flies south to join the fun and teach our 4-Day Network Forensics class at Black Hat USA.
Ah, summer– when hackers migrate to Las Vegas to renew friendships, obtain bleeding-edge training, and release their latest exploits and security research. Every year, LMG flies south to join the fun and teach our 4-Day Network Forensics class at Black Hat USA.
Our first night we stopped by the Black Hat Network Operations Center (NOC) to distract help Pope and Kevin as they finalized the network config.
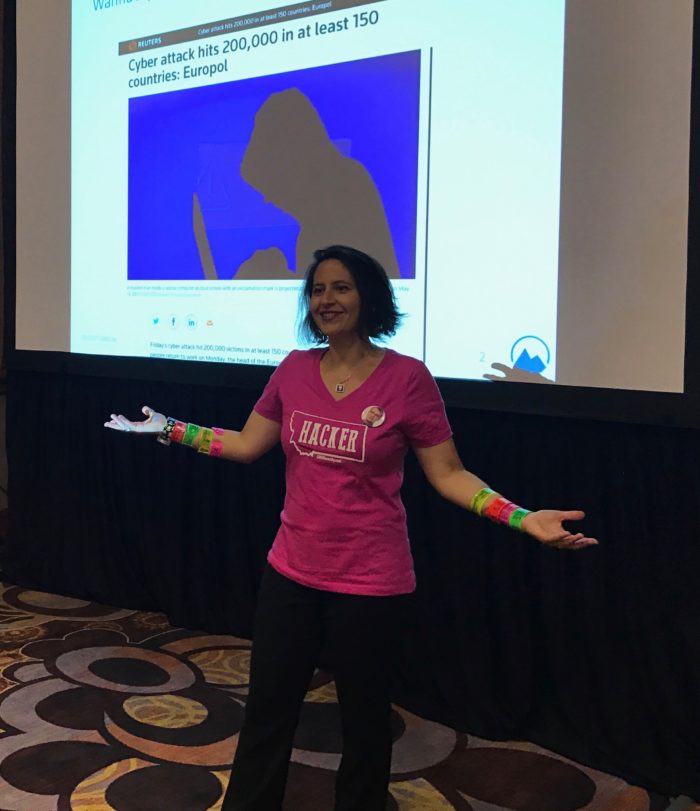
We kicked off the network forensics class in style! This year we gave students Cyber Slap bracelets with TCP/IP protocol charts, Linux command references, and more! That way students could wear super useful info conveniently on their wrists instead of having to flip back and forth to charts. Lots of people have been asking how to get a Cyber Slap Bracelet; we just put them online here.
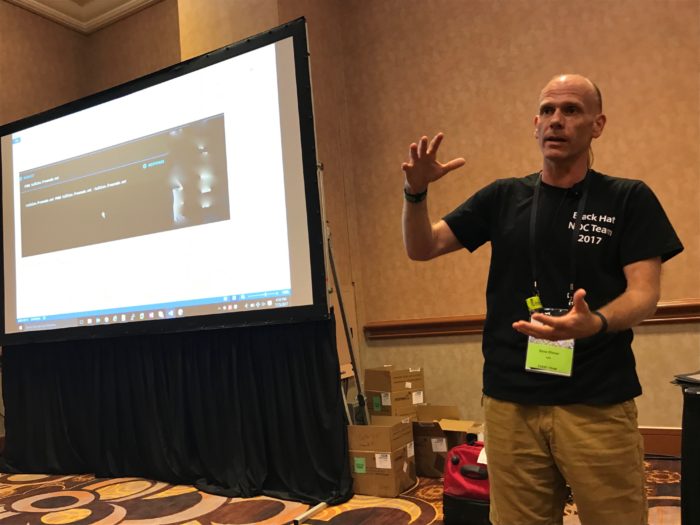
What better way to learn about network forensics than by studying the Black Hat network itself, live and in action? Black Hat NOC engineers Steve Fink and James Pope described the network architecture and how they keep packets flowing, even under the extreme conditions of Black Hat USA. Unlike most enterprises, the Black Hat NOC isn’t there to squash your malware– their goal is to enable classrooms of students to handle malware and powerful hacking tools safely and effectively.
NOC architect Steve Fink describes that battle between good and evil on Black Hat’s network:
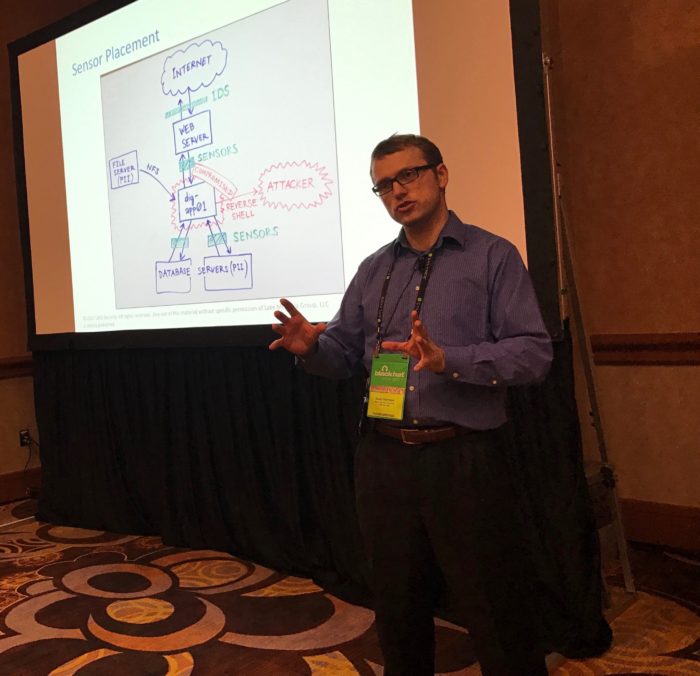
Where should you place your network sensors? David Harrison describes factors to consider during the Instrumentation and Architecture module on Day 1:
Ali Sawyer of LMG taught a new section of the Wireless Forensics module:

Sherri compared the WannaCry damage to the fallout from Nimda and CodeRed “back in the day.”:
On the last day we got a special treat– NOC engineers Eric Partington and Dave Glover analyzed OUR class’ traffic using RSA’s Netwitness, which was a core piece of the Black Hat network monitoring architecture this year. They provided great insight on strategies for approaching network monitoring, and illustrated important points such as the importance of integrating DHCP logs with higher-layer analysis tools.
Thanks to the NOC staff and especially the RSA team for giving our class a peek into your operations!
The best part of the trip was getting to hang out with our awesome Network Forensics students for our traditional dinner at Battista’s Hole in the Wall:
After class, we went to an excellent Cylance dinner party, and had the pleasure of getting to know their team. This was a highlight of the conference! Here’s Sherri and Stuart McClure on their way to the Black Hat VIP party (stopping to take a pic with a cute puppy dog).
Many thanks to our wonderful class, the Black Hat organizers, and all of our friends and colleagues that make Black Hat such an amazing event. See you next year!