Holiday Hackers: How AI Is Supercharging Seasonal Fraud—and What Your Organization Must Do Now

“Consumer security is corporate security these days,” said Sherri Davidoff, founder of LMG Security, during a recent Cyberside Chats episode. Criminals know this. And they’re timing their efforts strategically.
In the 10 days leading up to Thanksgiving, holiday bot traffic is expected to surge 520%, according to researchers at Adobe. This surge coincides with a broader explosion in AI-driven abuse. Akamai reports that AI bot activity has climbed 300% over the past year, now generating billions of automated requests per day and increasing far faster than traditional bot traffic.
All of this activity creates a giant credential-harvesting opportunity—and a direct enterprise security problem.
Scam Spotlight: The “Gorilla Cart” Credential Phish
Security researchers at Malwarebytes recently uncovered a convincing fake Home Depot promotion offering a “Free Gorilla Cart for $11.97.” It featured polished branding, a countdown timer, a fake survey, and a “shipping fee” checkout screen—all designed to capture email addresses, passwords, and payment data.
Here’s why consumer scams matter to enterprises: employees often reuse the same passwords across personal shopping sites and corporate systems. When someone enters their credentials into a scam like this, attackers can immediately feed those stolen details into automated tools that probe a wide range of corporate systems—from cloud email and SSO portals to VPNs and HR platforms—looking for a match or a pattern they can exploit. Even if the password isn’t identical, criminals use the stolen information to power password spraying, MFA fatigue, account recovery abuse, and other identity-driven intrusion techniques.
A simple retail-themed scam becomes a credential pipeline directed at your enterprise identity infrastructure.
Malvertising Joins the Holiday Threat Mix
Bitdefender Labs observed a surge in Halloween-themed scams this season, including fake Home Depot “Giant Skelly” giveaways, bogus Walmart candy promotions, and fraudulent Amazon costume surveys. These scams fade, but cybercriminals reuse the same methods year-round.
Criminals don’t rebuild new campaigns for Black Friday, Cyber Monday, and Christmas—they simply reskin and scale the same backend infrastructure, now fueled by AI-generated branding that can be updated instantly.
Bitdefender also observed malvertising campaigns during the lead-up to the holidays, including fake ads on Meta platforms that redirected users to trojanized TradingView apps. These poisoned ads blend in with legitimate seasonal deals, making it easy for employees to encounter them while browsing or shopping. Even a quick click from a personal or work device can expose the organization to credential theft or malware.
Implementing enterprise ad-blocking and DNS filtering can significantly reduce exposure by preventing malicious ads and redirect domains from ever reaching employees.
In The Lab: WormGPT Creates a Holiday Scam Site
One of the biggest changes this year is speed. Criminals can launch themed phishing campaigns in minutes—not days. At LMG Security, our researchers tested a malicious AI model, WormGPT, to see how easily it could produce holiday-themed phishing content. The results were sobering.
“WormGPT did in 30 seconds what used to take hours to build,” said Matt Durrin, LMG Security’s director of training. “It instantly created a holiday shopping scam that we could launch right now.”
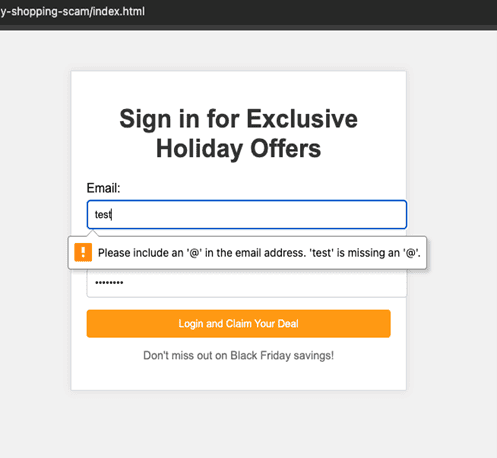
Screenshot of the scam website instantly generated by WormGPT in LMG’s laboratory. This clean, friendly page is designed to steal credentials.
Combined with real-time AI image generation and prebuilt “config” files for credential stuffing, attackers can rapidly reskin campaigns for:
- Black Friday
- Cyber Monday
- Christmas promotions
- Gift-card “specials”
- Fake charity drives
- Holiday returns and refund fraud
As demonstrated in LMG’s lab, AI now lets attackers mass-produce holiday scams faster than organizations can defend against them.
How Consumer Holiday Scams Turn into Enterprise Security Risks
Many CISOs ask, “Why does my enterprise care about holiday scams?”
Remember, consumer security is corporate security now. When attackers steal personal shopping credentials or compromise a home device, those risks flow straight into your enterprise environment through a few well-known pathways:
1. Password reuse spreads personal risk to the enterprise
Employees reuse passwords across Amazon, Costco, Target, personal email—and corporate systems. Attackers know this.
Automated bots harvest retail credentials, then test them against:
- SSO portals
- VPNs
- Microsoft 365
- HR systems
- Vendor portals
If passwords match—or are only slightly modified—criminals get in.
2. Compromised personal devices can provide a direct bridge into your enterprise
Attackers regularly gain corporate access by first compromising an employee’s personal phone or laptop. The 2022 Uber breach is a prime example: attackers stole credentials from a contractor’s personal device, used them to access the VPN, and then bypassed MFA using fatigue attacks. Personal devices used for work email, messaging, or authentication create the same exposure for any organization.
One poisoned ad or malicious search result can compromise a device connected to your corporate environment.
3. Attackers rapidly test stolen consumer credentials across corporate systems using automated tools
After harvesting large batches of usernames and passwords from holiday scams, attackers run them through automated credential-testing tools that probe SSO, VPN, Microsoft 365, HR, and payroll systems. They also use the stolen data for password spraying, trying common or pattern-based passwords against many enterprise accounts simultaneously. Even partial similarities in password habits can lead to access. A single stolen credential becomes the foundation for multiple identity-based attack paths.
4. Holiday workforce strain increases social engineering risk across all industries
Many organizations—not just retailers—rely on seasonal staff, contractors, or reduced holiday coverage. Help desks, finance teams, customer support, IT operations, and security staff are often stretched thin or working alongside temporary workers who haven’t received full security training. Attackers know this and time their scams accordingly, using holiday-themed phishing, fake invoices, fraudulent refund requests, and social engineering attempts when teams are distracted, understaffed, or operating with less oversight.
Defensive Steps You Should Take Now (Holiday Checklist Included)
To help organizations prepare, LMG Security created a free Holiday Fraud Defense Checklist with tactical steps your team can take immediately.
Download it here: LMG Holiday Fraud Defense Checklist (PDF)
Key actions include:
- Strengthen MFA everywhere—especially SSO, VPN, and admin access.
- Harden email and web filtering to block malicious ads, redirect chains, and spoofed domains.
- Monitor for unusual login patterns and spikes in automated traffic.
- Run a short, targeted awareness push for employees ahead of Black Friday and again before Christmas.
- Reinforce personal-to-corporate security messaging—employees must understand that their personal account hygiene affects enterprise risk.
Conclusion: Stop Holiday Credential Theft Before It Becomes Enterprise Compromise
Holiday scams aren’t just a consumer nuisance—they’re a pipeline feeding enterprise breaches. With AI-powered bots, reskinned phishing kits, and poisoned ads scaling faster than ever, the line between personal and corporate security has all but disappeared.
A few proactive measures before the holidays—tightening MFA, filtering malicious ads, monitoring for credential-testing spikes, and boosting staff awareness—can make all the difference.
If your organization wants help evaluating exposure or strengthening defenses ahead of the holiday season, contact us for penetration tests, phishing assessments, and incident response readiness exercises designed for modern enterprise environments.
Stay safe this holiday season—and remember: protecting your organization means protecting your people.
